Port Forwarding in Windows
Last Updated on Tuesday, 27 September 2016 07:37 Written by BiRU Tuesday, 27 September 2016 07:37
In Microsoft Windows, starting from Windows XP, there is a built-in ability to set up network ports forwarding (port forwarding). Due to it, any connection coming to any port can be forwarded to another local port or even to port on remote computer. Not necessarily that the system has a service listens on this port.
Port forwarding in Windows can be configured using Portproxy mode of the command Netsh. The syntax of this command is as follows:
netsh interface portproxy add v4tov4 listenaddress=localaddress listenport=localport connectaddress=destaddress connectport=destport
where
- listenaddress is a local ip address waiting for a connection
- listenport listening port (the connection is waited on it)
- connectaddress is an IP address or DNS name to which the connection will be forwarded
- connectport is a TCP port to which the connection from listenport is forwarded to
Suppose, that our task is to make the RDP service to respond on a non-standard port, for example 3340 (the port can be changed in the settings of the service, but we will use RDP to make it easier to demonstrate forwarding).
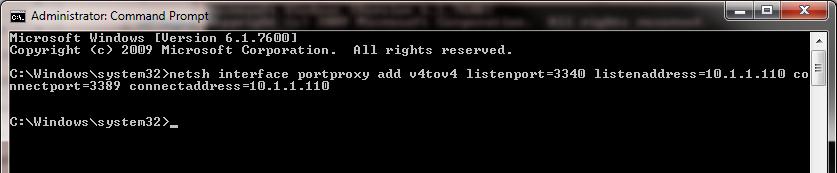
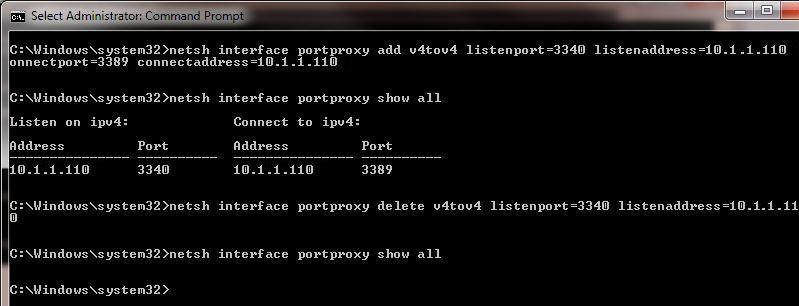
Start the command prompt as an administrator and perform the following command:
netsh interface portproxy add v4tov4 listenport=3340 listenaddress=10.1.1.110 connectport=3389 connectaddress=10.1.1.110
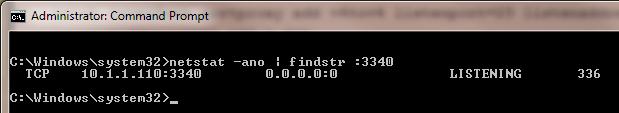
Using netstat make sure that port 3340 is listened now
netstat -ano | findstr :3340
You can find out what process is listening to this port use its PID (in our example, the PID is 336):
tasklist | findstr 336
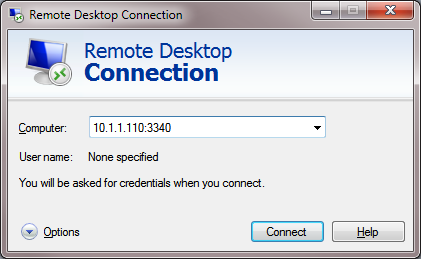
Let’s try to connect to this computer from a remote system using any RDP client. Port 3340 should be specified as the RDP port. (It is specified after the column following the RDP server address):
The connection should be established successful.
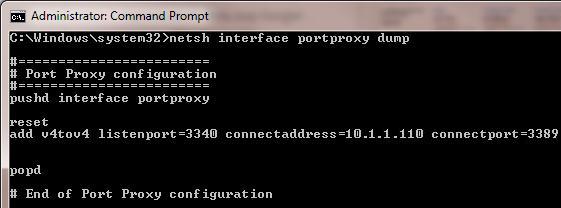
Display the list of forwarding rules in the system:
netsh interface portproxy show all
In our case there is only one forwarding rule from port 3340 to 3389:
Listen on ipv4: Connect to ipv4:
Address Port Address Port
--------------- ---------- --------------- ----------
10.1.1.110 3340 10.1.1.110 3389
To remove a forwarding rule:
netsh interface portproxy delete v4tov4 listenport=3340 listenaddress=10.1.1.110
To clear all current forwarding rules:
netsh interface portproxy reset
If you wont to forward an incoming TCP connection to another computer, the command can look like this:
netsh interface portproxy add v4tov4 listenport=3389 listenaddress=0.0.0.0 connectport=3389 connectaddress=192.168.100.101
This rule forwards all incoming RDP requests to the IP address 192.168.100.101
Another portproxy feature is an opportunity to make it look like any remote network service is operating locally.
For example, forward the connection from the local port 5555 to the remote address 157.166.226.25 (CNN website):
netsh interface portproxy add v4tov4 listenport=5555 connectport=80 connectaddress= 157.166.226.25 protocol=tcp
Now if you go to http://localhost:5555/ in your browser, CNN Start page will open. So despite the browser addresses the local computer, it opens a remote page.